Cyber Security
Most security problems are discovered too late
In many companies, security becomes a priority only after something goes wrong. As systems evolve - with new features, integrations, and infrastructure changes - vulnerabilities often remain unnoticed until they surface when the stakes are already high.
When companies start thinking about security
Security rarely becomes a priority by design. Most teams start asking serious questions only when a specific situation forces them to. These moments often reveal gaps that were previously unnoticed while the system was evolving.
Production incident
A vulnerability is discovered only after the system is already running in production.
This usually appears during an unexpected incident, suspicious activity, or potential data exposure. At that point, teams must investigate and fix the issue while the system is already serving users.
Client security review
A large client asks detailed questions about security practices.
They want to understand how your system protects data, whether penetration testing was performed, and how access control and monitoring are handled.
Investor due diligence
Security risks often surface during technical due diligence.
Investors want to understand whether the platform can scale safely and whether hidden risks exist in the architecture or infrastructure.
Where security risks usually hide
Security gaps rarely come from a single mistake. They usually appear gradually as the system evolves.
Common sources of risk include:
- Authentication and authorization logic that grew organically
- APIs exposing more data than intended
- Outdated or vulnerable third-party dependencies
- Cloud infrastructure configured without clear security boundaries
- Missing monitoring and audit trails
Why automated scans are not enough
Most security tools focus on known vulnerability patterns.
While useful, they rarely reveal risks related to system architecture, integration flows, or infrastructure configuration.
Understanding these issues requires engineers who analyze how the entire system works together.
What teams usually need at this stage
At this point, most teams are not looking for another automated scan.
They need:
- Clear visibility into real security risks
- Prioritization of vulnerabilities based on impact
- Architecture-level recommendations
- Practical roadmap for remediation
Our cybersecurity capabilities
We help companies secure modern software systems across the entire lifecycle – from architecture and development to testing and production hardening. Our services focus on identifying real risks and providing clear paths to remediation.
01
Application Security Audit
A comprehensive technical review of your application that identifies vulnerabilities across the codebase, dependencies, APIs, and infrastructure.
Focus areas include:
- code-level security vulnerabilities
- third-party dependency risks
- API security and exposure
- authentication and authorization logic
- data protection practices
02
Penetration Testing
Simulated real-world attacks designed to identify exploitable vulnerabilities before they can be used by attackers.
Focus areas include:
- web application security testing
- API penetration testing
- authentication and session security
- cloud infrastructure exposure
- input validation and injection risks
03
DevSecOps Implementation
Integrating automated security practices directly into the development and deployment pipeline.
Focus areas include:
- CI/CD security scanning
- dependency vulnerability monitoring
- container and image security
- secrets management
- automated security testing
04
Secure Architecture Design
Designing software systems where security is built into the architecture from the start.
Focus areas include:
- threat modeling
- identity and access management design
- encryption and key management strategies
- secure service communication
- cloud security architecture
05
Security Hardening
Preparing applications and infrastructure for secure production environments.
Focus areas include:
- infrastructure and network hardening
- API security controls
- logging and monitoring configuration
- access policy management
- production security best practices
How the Security Assessment Works
Our process is designed to quickly identify security risks and provide clear, actionable recommendations for your team.
01
Discovery
We start with a short discovery session to understand your system, architecture, and technology stack. This helps us identify the most important areas to review and align the assessment with your business context.
Typical topics include:
- system architecture overview
- technology stack and infrastructure
- critical integrations and APIs
- data sensitivity and compliance context
02
Technical Assessment
Our engineers perform a deep technical review of the application, infrastructure, and development practices. This phase combines manual analysis with targeted security testing to uncover vulnerabilities and architectural risks.
Focus areas include:
application code and dependencies
API exposure and authentication flows
infrastructure configuration
development pipeline security
03
Risk Analysis
We analyze the findings and prioritize vulnerabilities based on their real impact. Instead of presenting a long list of issues, we focus on the risks that could realistically affect your system and your business.
This includes:
vulnerability severity assessment
architectural risk identification
attack surface evaluation
prioritization of remediation work
05
Remediation Roadmap
You receive a clear and structured plan for addressing the identified risks. Our goal is to help your team move forward with practical steps rather than theoretical recommendations.
Deliverables typically include:
executive summary for leadership
technical vulnerability report
architecture risk overview
prioritized remediation roadmap
Not sure where your security risks are?
If you’re unsure how secure your application or infrastructure really is, a short conversation can help clarify where potential risks may exist and what steps are worth considering.
Speak directly with Radek Lejsza, COO of Codeflyers
Our clients' trust is our path.
We take great pride in the satisfaction of or clients, as evidence by their glowing feedback.
What our clients says about outcome of the collaboration?
We sent this question directly to our partners
Working with Codeflyers has been a game-changer for us! Their innovative approach and unparalleled technical expertise have propelled our project to new heights. We’re thrilled with the progress and their proactive attitude.
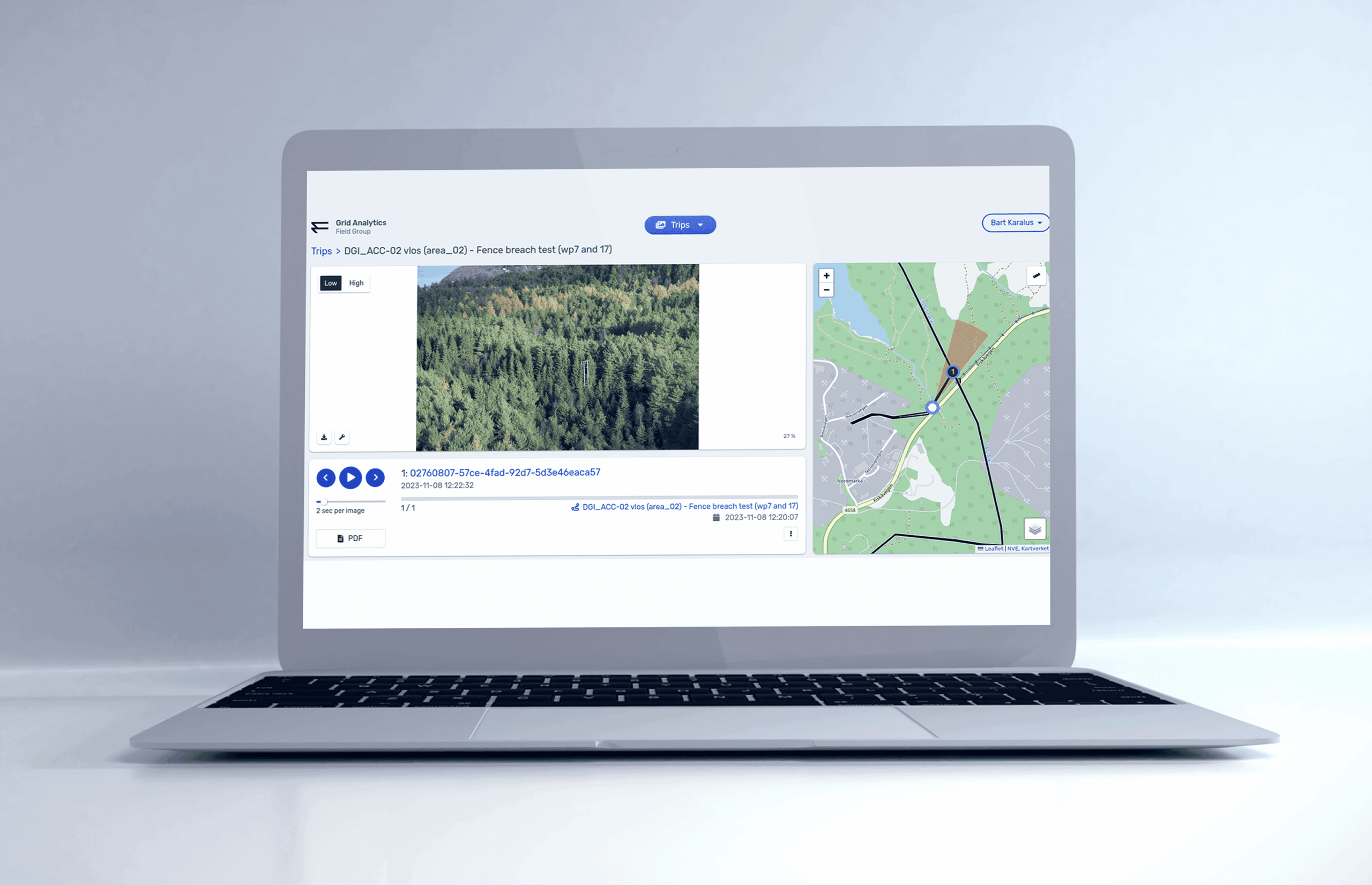
Christoffer Apneseth
CTO at Field
Our collaboration with Codeflyers is a perfect match! Their team is not only competent but also incredibly dedicated. The application is growing stronger, all thanks to their commitment and attention to detail.
Even Reitan
Strategy & Business Development Manager at Telenor
Not sure where your security risks are?
If you’re unsure how secure your application or infrastructure really is, a short conversation can help clarify where potential risks may exist and what steps are worth considering.
Speak directly with Radek Lejsza, COO of Codeflyers
Frequently asked questions
Clear answers to the questions we hear most often
How long does a security assessment take?
The timeline depends on the size and complexity of the system. Smaller applications can usually be assessed within a few days, while larger platforms or complex infrastructures may require a longer review.
Do you perform automated or manual security testing?
We combine automated tools with manual analysis performed by experienced engineers. Automated scanners help identify known vulnerabilities, while manual review allows us to detect architectural and integration risks that tools often miss.
What technologies and platforms do you support?
We work with modern software stacks and cloud environments, including web applications, APIs, microservices architectures, and major cloud platforms such as AWS, Azure, and Google Cloud.